Sandbox
➤ Introduction
This test environment can be used in 2 ways :
Try-it mode on 89C3 API portal (see use case "Try-it mode") ;
either directly via your app : this mode is described hereafter.
Fictive data are used in this context (see use case "Test with persona").
➤ Prerequisites
You have to declare your APP on our portal (menu "My applications") and to send us :
- your organisation agreement identifier (OID) as defined by your national competent authority ;
- the public keys of tour test QWAC & QSEALC eiDAS compliant certificates ;
- your callback uri (redirect_uri).
Reminder : you have to get your "AISP" agrement (or being in process of getting it).
➤ Step-by-step approach
1st step : request the access token
This token is mandatory to consume API resources.
This call triggers the PSU redirection towards his ASPSP. See the use case "Get your token".
Note : if the PSU has accounts in different ASPSP, you need one access token per ASPSP, and therefore, this request has to be used for each ASPSP.
Our entry point depends on ASPSP code : www.<cdetab>.sandbox.api.89C3.com , and for this environment, the only Caisse d'Epargne available is CE Ile de France with <codetab> = 17515.
Example :
GET https://www.17515.sandbox.api.89C3.com/stet/psd2/oauth/authorize
Headers :
Content-Type : application/x-www-form-urlencoded; charset=utf-8
Params:
response_type:code
client_id:PSDFR-ACPR-13807
redirect_uri:https://www.mycallback.com/
scope:aisp
Remark :
client_id : your organisation agreement identifier as defined by your national competent authority (PSDXX-YYYY-ZZZZZ).
redirect_uri : callback URL as declared in your APP AND to be forwarded to ASPSP for each sandbox and Go Live requests
2nd step : redirection to PSU screens
Once the redirection is activated, the ASPSP displays to PSU identification and authentification screens.
The UX is shown below :
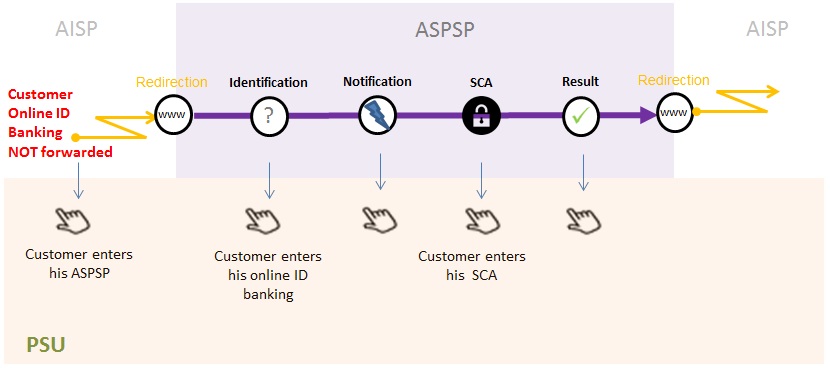
1) PSU can enter his online banking ID thru the identification screen displayed by the ASPSP.
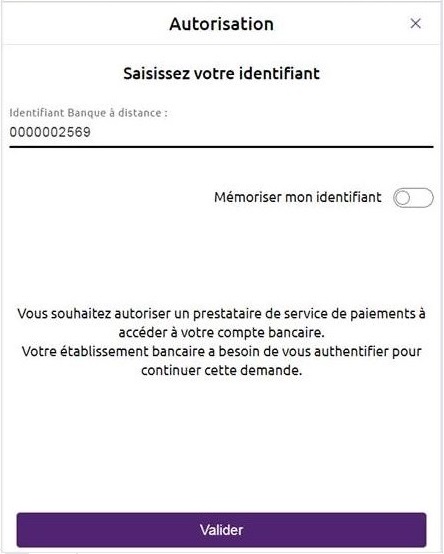
Note : if PSU is a professional or a corporate, another screen requesting the usage number can be displayed.
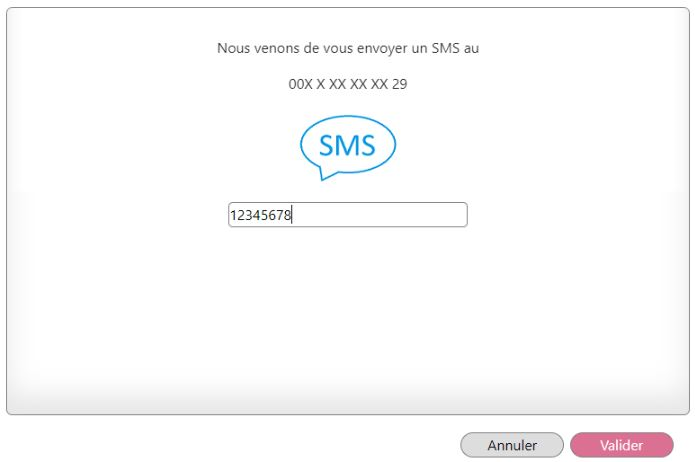
2) PSU needs to enter his SCA credentials in the authentication screen.
Different SCA means can be used by the PSU (SMS OTP - see below-, soft token, etc.) :
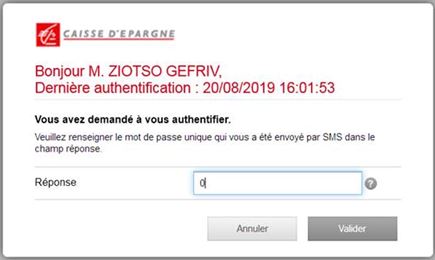
In some cases, a notification can be sent to the PSU on his/her mobile phone to activate his PSU means, or to finish this step :
3rd step : get the access token
You can get your access token to be able to consume API resources.
Please note that the QWAC certificate needs to be sent for TLS mutual authentication. This certificate has to be the same as the one declared :
- during the Go Live process on the 89C3 API portal
- or during the self-enrolment process using the API REGISTER (see https://www.api.89c3.com/en/component/bpceportal/products/543/usecases/533)
If the PSU has authorized the TPP to access to his payment account (successful SCA), a 1-hour validity unique code will be genereted. It will be used for requesting the access_token useful to consumme API methods (see use case "Get your token").
Example
POST https://www.17515.sandbox.api.89C3.com/stet/psd2/oauth/token
Header :
Content-Type:application/x-www-form-urlencoded; charset=utf-8
Params :
client_id:PSDFR-ACPR-13807
grant_type:authorization_code
code:NnZx1hqHY2CLkCFjiTwhJeflgFedCBa
redirect_uri:https://www.mycallback.com/
Remarks :
client_id : your agreement number as defined by your national competent authority (PSDXX-YYYY-ZZZZZ).
code : data in callback url
redirect_uri : this data needs to be strictly identical to the "redirect_uri" one used in the GET /authorize request !!!
The QWAC eiDAS certificate has to be sent with this request.
Response :
{
"access_token" : "KXZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoI0Kr2rSi1mSCFNehAbCdEf",
"token_type" : "Bearer",
"expires_in" : 3600,
"scope" : "aisp offline_access",
"refresh_token" : "KUZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoD0Kr2rSi1mSCFNewRfrsH"
}
4th step : use the API methods
1) Get the list of accounts
Once the acces token is received, this methods allows the TPP to list tha payment accounts during the first call (see use case "Get accounts list").
The TPP sequence is as follows :
- GET /accounts to list all available accounts (without any links nor balances neither transactions)
- ask PSU which accounts & data he wants to authorize TPP to get access to
- PUT /consents for sending to ASPSP the list of authorize accounts
- GET /accounts to access to authorized data
Example BEFORE the PUT /consents method:
GET https://www.17515.sandbox.api.89C3.com/stet/psd2/v1.4.2/accounts
Header :
Authorization: Bearer KXZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoI0Kr2rSi1mSCFNehAbCdEf
X-Request-ID: id-1234567890111121 1
Signature: keyId=\"https://<www.myUrlPath.to>/myQsealCertificate_<footprint sha256>\", algorithm=\"rsa-sha256\", headers=\"(request-target) psu-ip-address psu-ip-port psu-http-method psu-date psu-user-agent psu-referer psu-accept psu-accept-charset psu-accept-encoding psu-accept-language digest\", signature=\"LbkxgICM48J6KdWNaF9qT7OWEorNlAwWNo6R+KkP7cP4TIGkk8wxcsGQXJ9ZnC+ZiA8mjL5S8WQyL41M7iPt+vJX4xh679gdGwmlKzn7E+ZtZ1I4qalRxcdLp4gBL7fll+C2lVBNJrViMJBezFK7AYVjnSWH7t1QiMViAmthebEst=\"
Psu-IP-Address:192.168.0.1
No body
Remarks :
Psu-Ip-Address => allows to differentiate batch request triggered by the TPP from requests whenever connected PSU to TPP app : so this field has to be filled when the PSU is connected
Response : 200 OK
Headers :
X-Request-ID:id-1234567890111121 1
Body :
{
"_links": {
"self": {
"templated": false,
"href": "/stet/psd2/v1.4.2/accounts"
}
},
"accounts": [
{
"cashAccountType": "CACC",
"accountId": {
"iban": "FR7617515000920400430518020"
},
"usage": "PRIV",
"psuStatus": "Account Holder",
"name": "LEA SANDBOXA",
"currency": "EUR"
},
{
"cashAccountType": "CACC",
"accountId": {
"iban": "FR7617515000920400851811524"
},
"usage": "PRIV",
"psuStatus": "Account Holder",
"name": "LEA SANDBOXA",
"currency": "EUR"
}
]
}
Example AFTER the PUT /consents method:
GET https://www.17515.sandbox.api.89C3.com/stet/psd2/v1.4.2/accounts
Header :
Authorization: Bearer KXZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoI0Kr2rSi1mSCFNehAbCdEf
X-Request-ID: id-1234567890111121 1
Signature: keyId=\"https://<www.myUrlPath.to>/myQsealCertificate_<footprint sha256>\", algorithm=\"rsa-sha256\", headers=\"(request-target) psu-ip-address psu-ip-port psu-http-method psu-date psu-user-agent psu-referer psu-accept psu-accept-charset psu-accept-encoding psu-accept-language digest\", signature=\"LbkxgICM48J6KdWNaF9qT7OWEorNlAwWNo6R+KkP7cP4TIGkk8wxcsGQXJ9ZnC+ZiA8mjL5S8WQyL41M7iPt+vJX4xh679gdGwmlKzn7E+ZtZ1I4qalRxcdLp4gBL7fll+C2lVBNJrViMJBezFK7AYVjnSWH7t1QxinDocH1ne=\"
Psu-IP-Address:192.168.0.1
No body
Remarks :
Psu-Ip-Address => allows to differentiate batch request triggered by the TPP from requests whenever connected PSU to TPP app : so this field has to be filled when the PSU is connected
Response : 200 OK
Headers :
X-Request-ID:id-1234567890111121 2
Body
{
"_links": {
"self": {
"templated": false,
"href": "/stet/psd2/v1/accounts"
}
},
"accounts": [
{
"cashAccountType": "CACC",
"accountId": {
"iban": "FR7617515000920400430518020"
},
"resourceId": "175150009204004305180",
"_links": {
"balances": {
"templated": false,
"href": "/stet/psd2/v1/accounts/175150009204004305180/balances"
},
"transactions": {
"templated": true,
"href": "/stet/psd2/v1/accounts/175150009204004305180/transactions"
}
},
"usage": "PRIV",
"psuStatus": "Account Holder",
"name": "LEA SANDBOXA",
"currency": "EUR"
},
{
"cashAccountType": "CACC",
"accountId": {
"iban": "FR7617515000920400851811524"
},
"resourceId": "175150009204008518115",
"_links": {
"balances": {
"templated": false,
"href": "/stet/psd2/v1/accounts/175150009204008518115/balances"
},
"transactions": {
"templated": true,
"href": "/stet/psd2/v1/accounts/175150009204008518115/transactions"
}
},
"usage": "PRIV",
"psuStatus": "Account Holder",
"name": "LEA SANDBOXA",
"currency": "EUR"
}
]
}
2) Send PSU consent to ASPSP
See use case "Forward PSU consent".
Example :
PUT https://www.17515.sandbox.api.89C3.com/stet/psd2/v1.4.2/consents
Headers :
Authorization: Bearer KXZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoI0Kr2rSi1mSCFNehAbCdEf
X-Request-ID: id-1234567890111121 2
Signature: keyId=\"https://<www.myUrlPath.to>/myQsealCertificate_<footprint sha256>\", algorithm=\"rsa-sha256\", headers=\"(request-target) psu-ip-address psu-ip-port psu-http-method psu-date psu-user-agent psu-referer psu-accept psu-accept-charset psu-accept-encoding psu-accept-language digest\", signature=\"LbkxgICM48J6KdWNaF9qT7OWEorNlAwWNo6R+KkP7cP4TIGkk8wxcsGQXJ9ZnC+ZiA8mjL5S8WQyL41M7iPt+vJX4xh679gdGwmlKzn7E+ZtZ1I4qalRxcdLp4gBL7fll+C2lVBNJrViMJBezFK7AYVjnSWH7t1QinCept10n=\"
Psu-IP-Address:192.168.0.1
Body
{
"balances": [
{
"iban": "FR7617515000920400430518020"
},
{
"iban": "FR7617515000920400851811524"
}
],
"transactions": [
{
"iban": "FR7617515000920400430518020"
},
{
"iban": "FR7617515000920400851811524"
}
],
"trustedBeneficiaries": false,
"psuIdentity": false
}
Response :
201 « Created »
Headers :
X-Request-ID:id-1234567890111121 2
No body
3) Get the balances
See use case "Accounting balances".
Example :
GET https://www.17515.sandbox.api.89C3.com/stet/psd2/v1.4.2/accounts/{accountResourceId}/balances
Headers :
Authorization: Bearer KXZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoI0Kr2rSi1mSCFNehAbCdEf
X-Request-ID: id-1234567890111121 2
Signature: keyId=\"https://<www.myUrlPath.to>/myQsealCertificate_<footprint sha256>\", algorithm=\"rsa-sha256\", headers=\"(request-target) psu-ip-address psu-ip-port psu-http-method psu-date psu-user-agent psu-referer psu-accept psu-accept-charset psu-accept-encoding psu-accept-language digest\", signature=\"LbkxgICM48J6KdWNaF9qT7OWEorNlAwWNo6R+KkP7cP4TIGkk8wxcsGQXJ9ZnC+ZiA8mjL5S8WQyL41M7iPt+vJX4xh679gdGwmlKzn7E+ZtZ1I4qalRxcdLp4gBL7fll+C2lVBNJrViMJBezFK7AYVjnSWH7t1Qincept10n=\"
Response :
200 OK
Headers :
X-Request-ID:id-1234567890111121 2
Body :
{
"balances": [
{
"balanceType": "CLBD",
"name": "Solde comptable au 28/09/2018",
"balanceAmount": {
"amount": "-150.00",
"currency": "EUR"
}
}
],
"_links": {
"self": {
"templated": false,
"href": "/stet/psd2/v1/accounts/175150009204004305180/balances"
},
"transactions": {
"templated": true,
"href": "/stet/psd2/v1/accounts/175150009204004305180/transactions"
},
"parent-list": {
"templated": false,
"href": "/stet/psd2/v1/accounts"
}
}
}
4) Get transactions history
See use case "Get transactions history".
Example :
GET https://www.17515.sandbox.api.89C3.com/stet/psd2/v1.4.2/accounts/{accountResourceId}/transactions
Headers :
Authorization: Bearer KXZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoI0Kr2rSi1mSCFNehAbCdEf
X-Request-ID: id-1234567890111121 1
Signature: keyId=\"https://<www.myUrlPath.to>/myQsealCertificate_<footprint sha256>\",algorithm=\"rsa-sha256\",headers=\"(request-target) psu-ip-address psu-ip-port psu-http-method psu-date psu-user-agent psu-referer psu-accept psu-accept-charset psu-accept-encoding psu-accept-language digest\",signature=\"LbkxgICM48J6KdWNaF9qT7OWEorNlAwWNo6R+KkP7cP4TIGkk8wxcsGQXJ9ZnC+ZiA8mjL5S8WQyL41M7iPt+vJX4xh679gdGwmlKzn7E+ZtZ1I4qalRxcdLp4gBL7fll+C2lVBNJrViMJBezFK7AYVjnSWH7t1T0tOtuTuT1ti=\"
Psu-IP-Address:192.168.0.1
No body
Response :
200 OK
Headers :
X-Request-ID:id-1234567890111121 1
Body
{
"_links": {
"balances": {
"templated": false,
"href": "/stet/psd2/v1/accounts/175150009204004305180/balances"
},
"self": {
"templated": true,
"href": "/stet/psd2/v1/accounts/175150009204004305180/transactions"
},
"parent-list": {
"templated": false,
"href": "/stet/psd2/v1/accounts"
}
},
"transactions": [
{
"resourceId": null,
"remittanceInformation": [
"Retrait Carte"
],
"entryReference":"751040043051802019-09-08-05.33.46.621234",
"transactionAmount": {
"amount": "13.00",
"currency": "EUR"
},
"bookingDate": "2019-09-05",
"creditDebitIndicator": "DBIT",
"status": "BOOK"
}
]
}
5) Get PSU Identity
See use case "Get PSU identity".
Example :
GET https://www.12579.sandbox.api.89C3.com/stet/psd2/v1.4.2/end-user-identity
6) Refresh your access token
See use case "Refresh your token".
Example :
POST https://www.12579.sandbox.api.89C3.com/stet/psd2/oauth/token
Header :
Content-Type : application/x-www-form-urlencoded; charset=utf-8
Params:
client_id:PSDFR-ACPR-13807
grant_type:refresh_token
refresh_token:KUZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoD0Kr2rSi1mSCFNehAbCdEf
Response :
{
"access_token" : "4s2Bt3MRL7nlPUZcRTPe5Tjs0v8p7ZOXOyEKs1juYesR2bel0t3v1aAp1s",
"token_type" : "Bearer",
"expires_in" : 3600,
"scope" : "aisp offline_access",
"refresh_token" : "KUZyspFBZ1R6NqWQdmsZhfdo1nbjK7MoD0Kr2rSi1mSCFNehAbCdEf"
}